There are new government ministries in South Korea and the United States which are specifically designed to help protect government and important web sites against distributed denial-of-service (DDoS) attacks now. Millions of dollars and hundreds of man-hours are being spent to protect large companies from a future DDoS attack without loss of connection. But for the average small business or individual, this is not much help. What can you do specifically to protect against a DDoS attack
There are two potential events here that you will have to consider. The first is what to do to protect against being the target of a DDoS attack. The second is what to do to protect against being an unwitting participant in a DDoS attack. The former is far less likely, while the latter is more important for small-time players on the Internet stage.
Mechanics of a DDoS
Before we discuss how to protect against at DDoS attack, we should define exactly what it is. A DDoS, or distributed denial of service attack, is an evolution of an older type of attack, a denial of service attack. The principle is that while everyone has a connection to the Internet, these connections have limits to the amount of simultaneous communication connections they can handle, called bandwidth. This bandwidth is always divided into incoming and outgoing communication traffic, but they both use the same resources. If, for some reason, too many computers connect to one other computer on the Internet at the same time, they will take up a large portion of the total available bandwidth for that one computer. If the number of other computers trying to communicate with the one other computer is too great, then all of the bandwidth available to one computer becomes dedicated to receiving communications, and the computer is unable to send any communications out.
This can happen spontaneously. If a small web site is hosted on a small amount of bandwidth and it suddenly becomes popular a large number of legitimate users will begin to access the web site at the same time, causing the same effect as a denial-of-service attack. Because too many people are trying to access a web page that is not prepared for them, no one will be able to see the web page, and its popularity will die out quickly. This is the good kind of denial of service that anyone with a web page running ads wishes for, because it means money.
But, this can also be simulated by a hacker with a grudge. In a normal, old-school denial of service attack, a hacker will write a small script that repeatedly tries to connect with a web page. Computers open communications channels in much the same way people do, only faster. There is an opening hello, with a response hello. Then, communication begins. The web page, being an accommodating sort, will try to answer the connection hello with a hello of its own and reserve space to listen to the response. The hacker's computer, however, will not respond in the normal fashion and just try to open new connections. If the hacker's computer is faster and has more bandwidth available to it than the web site, it will begin to slow down the site. This is what hackers did in the 1990s, mostly for fun or because of a minor grievance.
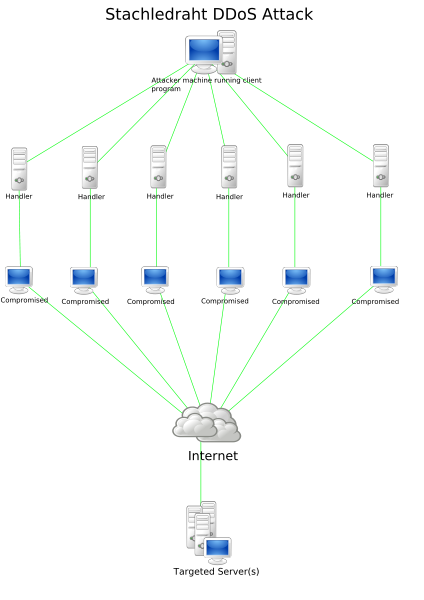
Then someone took it to the next level. Instead of using just one computer to needlessly bother a target web site, an enterprising hacker wrote a virus that spread to many other computers and caused them to start doing the same thing he was doing - feigning interest in the web site while and not responding to communications. It was as if one person was surrounded by a gang of others who just kept saying "Hello! Hello! Hello!" without listening to the replies. Its incapacitating. That is today's DDoS attack. It's not elegant, it's not sophisticated, it is just a bunch of digital shouting. So, how can you protect against a chorus of digital shouters
Against DDoS
If you're the target of a DDoS attack, there isn't much that you can personally do. If you are not a large company or government agency, you probably only have a small Internet presence hosted by your friendly neighborhood Internet Service Provider (ISP). This would be a blog or a web page, hopefully both, which might anger someone with too much time on their hands. If they were to attack you with a DDoS attack, it would be almost entirely up to your ISP what happens.
If your ISP is a quality company and cares about its customers, it will take the attack personally and start to filter traffic. The ISP probably has a thousand other customers who might be affected by the attack, and so responding to the attack as soon as possible will be in its best interest. If the company is worth the money you're paying it, they will have the software and capabilities to filter out the offending traffic by simply blocking the computers participating in the attack, or by blocking a certain type of connection request.
If your ISP is not a quality company, it will shut down your web page in order to avoid having to deal with the whole issue. In that case, you will have no choice but to migrate your site to a new host. Hopefully you can get some sort of refund for your trouble.
Against Participating in DDoS
The more likely scenario is that your home or office computer will be the unwitting participant in a DDoS attack. This can happen if your computer has been compromised by a virus which follows the orders of a hacker. The best way to avoid this scenario is to avoid getting viruses on your computer.
Avoiding viruses is a product of a user's good computer habits. Most computer viruses count on the computer user doing something foolish to spread, because automated systems are pretty secure against virus propagation. A virus will usually be spread as a computer program which shows up as an email attachment or an interesting thing to download on a web site. A careless user will run the program from email or downloads without making sure it is from a trusted source. The virus executes, copies itself all over the user's system, and turns over partial control of the system to the original virus writer, who can then use it in a DDoS attack.
In order to avoid this happening, the most effective solution is to make sure that the executable files, .exe files, come from sources you trust. Most legitimate people these days will not send .exe files to you, simply because it looks too suspicious. A cautious computer user will simply never download or run an .exe file that he receives by email. Also, a cautious computer user will only download .exe files from trusted web sites, like Microsoft.com or worldofwarcraft.com.
In order to protect from user errors, it is also always a good idea to run a virus scanner in the background. You can even download free virus scanners from the Internet, such as AVG. Every computer that you use should be running a virus scanner in order to avoid possible mistakes that you make.
If every computer user in the world followed these two simple rules, hackers would find a very barren field from which they could raise an army of DDoS-capable computers. But as things stand now, the Internet is a fertile ground of unsecured computers operated by careless users. Don't be one of them - keep your computer entirely in your hands with these two simple steps.


